Latest Elections News
On night 18/19 February 2026, Security Forces conducted a...
Statement Posted on 2 weeks ago Source: Correspondent "On night 18/19 February 2026, Securit...

MacBook Neo benchmark results are predictably close to iP...
Apple announced the MacBook Neo with the A18 Pro iPhone processor, and early benchmarks reveal ex...

Malkin ejected for slashing Dahlin in face - theScore.com
Pittsburgh Penguins forward Evgeni Malkin was handed a five-minute major and a game misconduct fo...

Here’s how the new M5 Max chip did on early Geekbench tes...
While the new M5 Pro and M5 Max MacBook Pros wont be available until March 11, the first M5 Max b...

How knitting can help you kick harmful habits - BBC
Casey, 60, a technology manager in California who asked us not to use her full name, tells the BB...

On 21 February, in a cowardly attack, Security Forces con...
Statement Posted on 2 weeks ago Source: Correspondent "On 21 February, in a cowardly attack,...
Elections Analysis

On 22 February 2026, security forces conducted an intelligence-based operation i...
Statement Posted on 2 weeks ago Source: Correspondent "On 22 February 2026, security forces conducted an intelligence-based operation in Pishin District of Balochistan, on reported presence of...
Analysis by News Desk
Read Analysis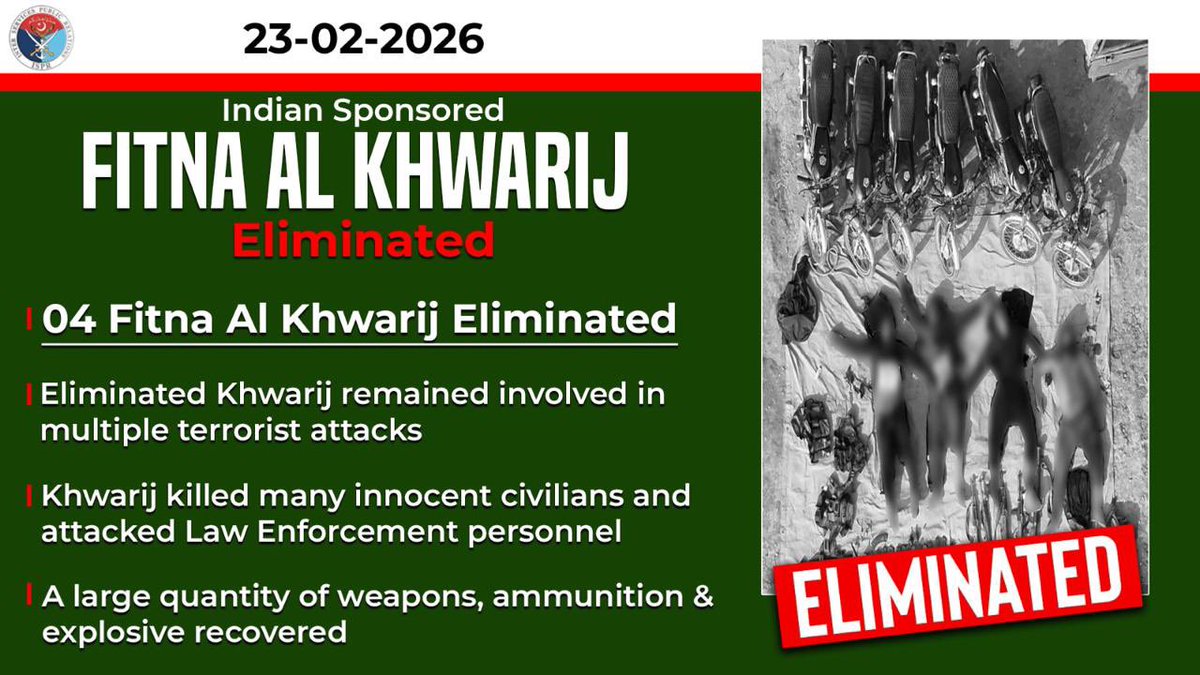
Security Forces Strike in Dera Ismail Khan: Four Militants Neutralized in Intelligence-Based Operation
On 23 February 2026, security forces conducted an intelligence-based operation in Dera Ismail Khan District following reports of Khawarij militants belonging to Indian proxies linked to the group F...
Analysis by News Desk
Read Analysis
Security Forces Intensify Counter-Terrorism Campaign in Pakistan: Recent High-Tempo Operations Target Indian-Backed Groups
Over the past days, Pakistan's Security Forces conducted a series of intelligence-driven operations as part of a relentless counter-terrorism campaign. In Khyber Pakhtunkhwa, 26 individuals li...
Analysis by News Desk
Read Analysis
Bitcoin exchange reserves just hit a level not seen since the Trump midterms
Centralized exchanges now hold fewer than 2.708 million BTC a supply squeeze not seen since November 2018. The amount of Bitcoin sitting on centralized exchanges just dropped below 2.708 million BT...
Analysis by Estefano Gomez
Read Analysis
Microsoft Reveals ClickFix Campaign Using Windows Terminal to Deploy Lumma Stealer
Microsoft on Thursday disclosed details of a new widespread ClickFix social engineering campaign that has leveraged the Windows Terminal app as a way to activate a sophisticated attack chain and de...
Analysis by [email protected] (The Hacker News)
Read AnalysisElections Statistics
1982
Total Articles