Latest Technology News
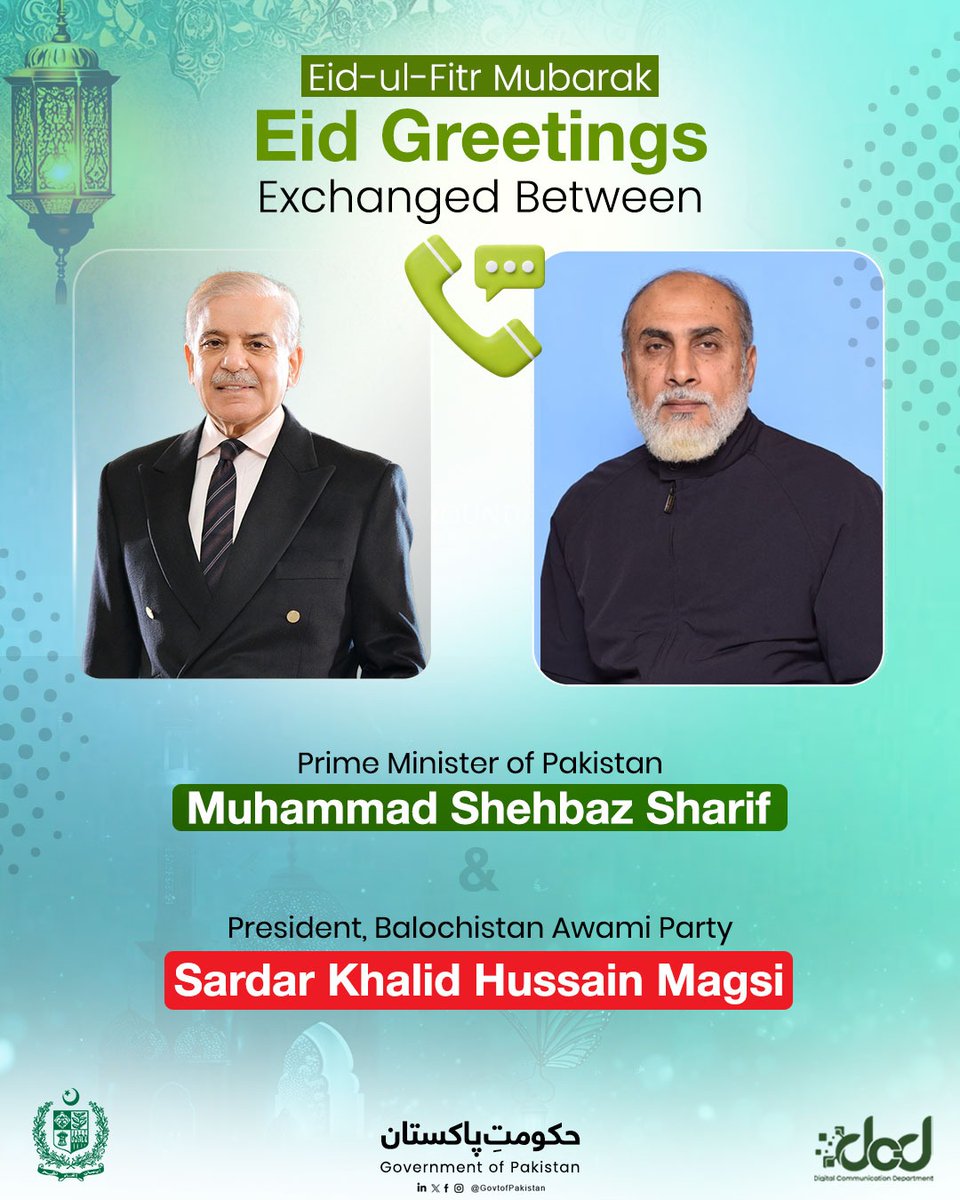
PM Shehbaz Sharif Reaffirms Cooperation with BAP Presiden...
Prime Minister Muhammad Shehbaz Sharif spoke by telephone with Sardar Khalid Hussain Magsi, presi...

BLA/BLF Attack at Eid Procession: Militants Seize Crowds ...
According to reports, armed militants affiliated with the Baloch Liberation Army (BLA) seized con...

ISPR Rawalpindi, 21 March 2026: Field Marshal Syed Asim M...
Field Marshal Syed Asim Munir, NI (M), HJ, COAS & CDF, visited Kurram to spend Eid-ul-Fitr wi...
Eid Greetings to Bahrain, Condemnation of Regional Hostil...
Pakistan's leader spoke with His Majesty King Hamad bin Isa Al Khalifa to convey warm Eid al...
BREAKING: Security forces thwart terrorist plot in Baloch...
In a developing breaking news report, security forces in Balochistan acted on intelligence about ...

Two Major Counter-Terrorism Operations in Balochistan Del...
Pakistan's security forces conducted two simultaneous, high-impact counter-terrorism operati...
Technology Analysis

iOS 26.3.1 (a): Apple’s Hidden iPhone Update Recommended For Hundreds Of Millions Of Users - Forbes
AFP via Getty Images This post, first published on Wednesday, March 18, was updated on Thursday, March 19 with more information about the first Background Security Improvement update. Apple release...
Analysis by David Phelan
Read Analysis
'Apparently Not Good Enough for Investors' Crimson Desert Publisher Stock Price Plunges Nearly 30% Amid 78 Metacritic Score - IGN
Pearl Abyss, publisher and developer of Crimson Desert, has seen its stock price plunge nearly 30% in what is seen as a reaction to review scores. Reviews for the hotly anticipated open-world actio...
Analysis by Wesley Yin-Poole
Read Analysis
Switch 2 Handheld Boost Mode Battery Life Sucks But Is Worth It - Kotaku
Nintendo rolled out a nice surprise for Switch 2 owners earlier this week. It’s called Handheld Boost Mode, and it runs Switch 1 games as if they were docked, even while in handheld mode. Sounds st...
Analysis by Ethan Gach
Read Analysis
Firefox Is Adding a Free Built-In VPN. Here's What It Means for You - CNET
Mozilla is updating Firefox with the addition of a free VPN service built into the web browser, confirming reports we first heard about last year. Firefox VPN has been available as a stand-alone pa...
Analysis by See full bio
Read Analysis
54 EDR Killers Use BYOVD to Exploit 34 Signed Vulnerable Drivers and Disable Security - The Hacker News
A new analysis of endpoint detection and response (EDR) killers has revealed that 54 of them leverage a technique known as bring your own vulnerable driver (BYOVD) by abusing a total of 35 vulnerab...
Analysis by The Hacker News
Read Analysis
