Latest Cricket News
Summary of Eid greetings and solidarity discussion with K...
A formal dialogue in which the speaker conveyed warm Eid-ul-Fitr greetings to His Majesty King Ab...

DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for F...
A new exploit kit for Apple iOS devices designed to steal sensitive data from is being wielded by...

Crimson Desert Devs Share Price Crashes Following Review ...
Pearl Abyss has suffered a 29% plunge in share value as the review scores for Crimson Desert emer...

Clashes Erupt in Bara Hours After Ceasefire Announcement
Heavy fighting between militants and Pakistani security forces continues in Bara, Khyber, with he...

DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for F...
A new exploit kit for Apple iOS devices designed to steal sensitive data from is being wielded by...

Crypto.com Slashes Workforce by 12% in 'Enterprise-Wide A...
In brief Crypto.com is reducing its workforce by 12%, affecting approximately 180 employeesCEO Kr...
Cricket Analysis

A DarkSword hangs over unpatched iPhones
Researchers at Google have identified an iOS exploit chain, named DarkSword, that has been used since late last year by multiple actors to infect iPhones with malware in targeted attacks. DarkSword...
Analysis by parntz
Read Analysis
Ethereum long squeeze risk rises as ETH price dips to $2,100
Ether (ETH) traded lower on Thursday after a fresh knee-jerk reaction to yesterdays US interest rate decision and a higher inflation outlook. Key takeaways: ETH dropped 7% to $2,100 on Thur… [+4063...
Analysis by Cointelegraph by Nancy Lubale
Read AnalysisBTCC Exchange Reports 135% Total Reserves for March 2026 as TradFi Commodity Volume Tops $144 Million
A Media Snippet accompanying this announcement is available by clicking on this link. LODZ, Poland, March 19, 2026 (GLOBE NEWSWIRE) -- BTCC, the world's longest-serving cryptocurrency exchange...
Analysis by BTCC LIMITED
Read Analysis
Crypto.com lays off 12% of workforce in latest company to cite AI in job cuts
Cryptocurrency trading platform Crypto.com announced Thursday that it is laying off 12% of its staff as the company integrates artificial intelligence. "We are joining the list of companies in...
Analysis by Lola Murti
Read Analysis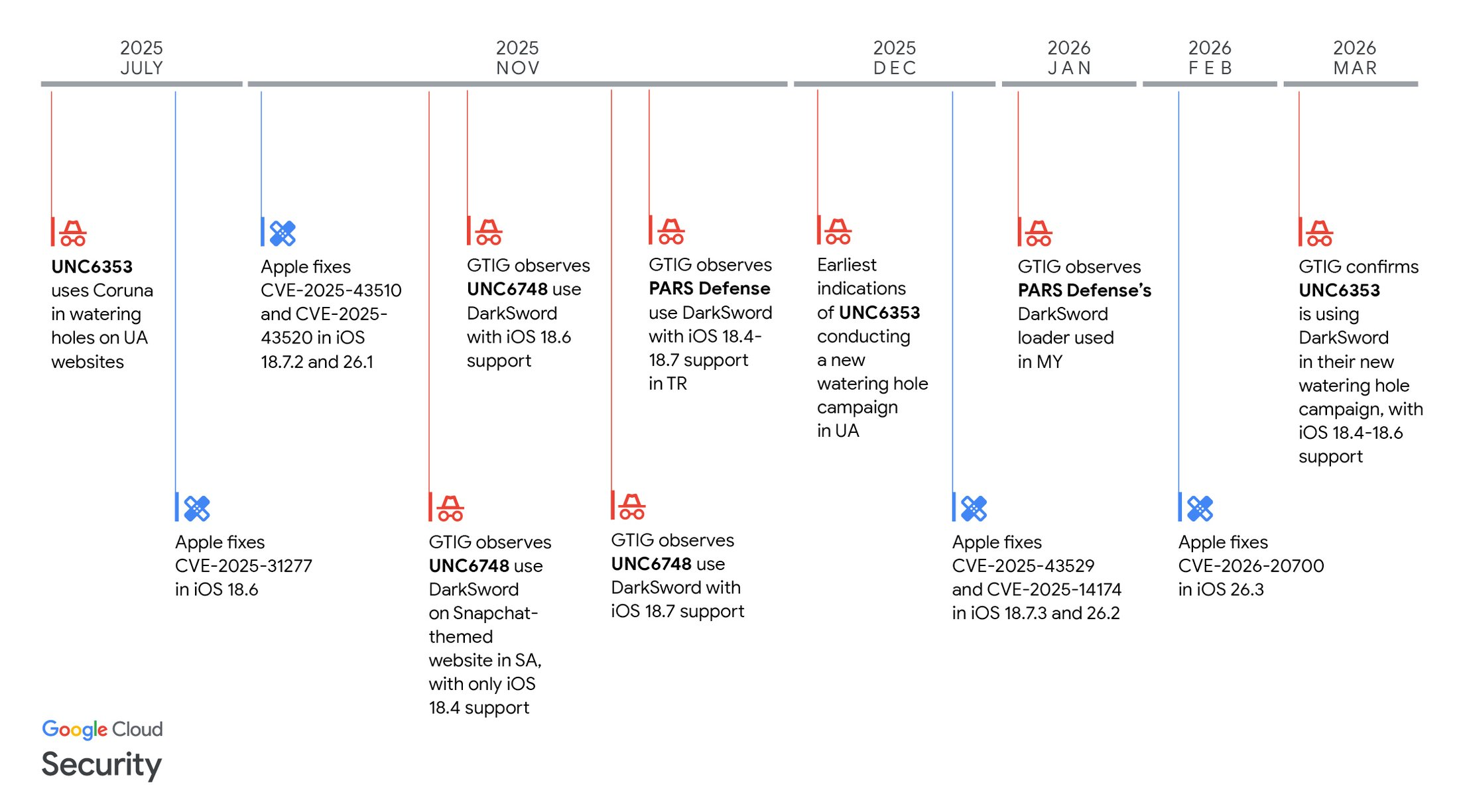
DarkSword emerges as powerful iOS exploit tool in global attacks
DarkSword emerges as powerful iOS exploit tool in global attacks Lookout Threat Labs discovered a new iOS exploit kit called DarkSword that has been used since late 2025 by multiple threat actors, ...
Analysis by Pierluigi Paganini
Read AnalysisCricket Statistics
5799
Total Articles